21. Topic 3, Litware Inc.
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam time as you would like to complete each case. However, there may be additional case studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button. Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. If the case study has an All Information tab, note that the information displayed is identical to the information displayed on the subsequent tabs. When you are ready to answer a question, click the Question button to return to the question.
Overview
General Overviews
Litware, Inc. is a technology research company. The company has a main office in Montreal and a branch office in Seattle.
Environment
Existing Environment
The network contains an on-premises Active Directory domain named litware.com.
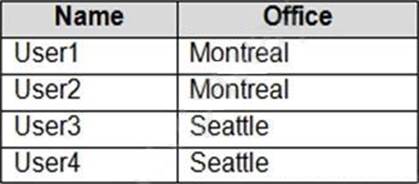
The domain contains the users shown in the following table.
Microsoft Cloud Environment
Litware has a Microsoft 365 subscription that contains a verified domain named litware.com. The subscription syncs to the on-premises domain.
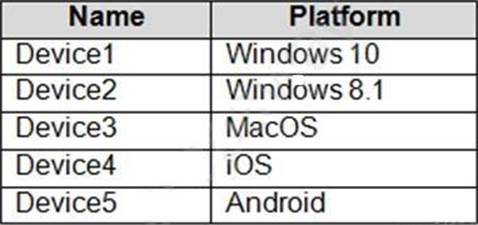
Litware uses Microsoft Intune for device management and has the enrolled devices shown in the following table.
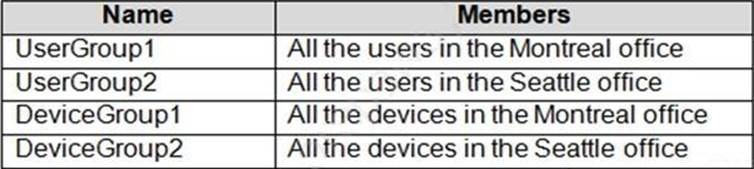
Litware.com contains the security groups shown in the following table.
Litware uses Microsoft SharePoint Online and Microsoft Teams for collaboration.
The verified domain is linked to an Azure Active Directory (Azure AD) tenant named litware.com. Audit log search is turned on for the litware.com tenant.
Problem Statements
Litware identifies the following issues:
✑ Users open email attachments that contain malicious content.
✑ Devices without an assigned compliance policy show a status of Compliant.
✑ User1 reports that the Sensitivity option in Microsoft Office for the web fails to appear.
✑ Internal product codes and confidential supplier ID numbers are often shared during Microsoft Teams meetings and chat sessions that include guest users and external users.
Requirements
Planned Changes
Litware plans to implement the following changes:
✑ Implement device configuration profiles that will configure the endpoint protection template settings for supported devices.
✑ Configure information governance for Microsoft OneDrive, SharePoint Online, and Microsoft Teams.
✑ Implement data loss prevention (DLP) policies to protect confidential information.
✑ Grant User2 permissions to review the audit logs of he litware.com tenant.
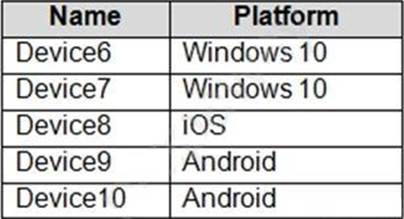
✑ Deploy new devices to the Seattle office as shown in the following table.
✑ Implement a notification system for when DLP policies are triggered.
✑ Configure a Safe Attachments policy for the litware.com tenant.
Technical Requirements
Litware identifies the following technical requirements:
✑ Retention settings must be applied automatically to all the data stored in SharePoint Online sites, OneDrive accounts, and Microsoft Teams channel messages, and the data must be retained for five years.
✑ Emails messages that contain attachments must be delivered immediately, and placeholder must be provided for the attachments until scanning is complete.
✑ All the Windows 10 devices in the Seattle office must be enrolled in Intune automatically when the devices are joined to or registered with Azure AD.
✑ Devices without an assigned compliance policy must show a status of Not Compliant in the Microsoft Endpoint Manager admin center.
A notification must appear in the Microsoft 365 compliance center when a DLP policy is triggered.
User2 must be granted the permissions to review audit logs for the following activities:
- Admin activities in Microsoft Exchange Online
- Admin activities in SharePoint Online
- Admin activities in Azure AD
Users must be able to apply sensitivity labels to documents by using Office for the web.
Windows Autopilot must be used for device provisioning, whenever possible.
A DLP policy must be created to meet the following requirements:
- Confidential information must not be shared in Microsoft Teams chat sessions, meetings, or channel messages.
- Messages that contain internal product codes or supplier ID numbers must be blocked and deleted.
The principle of least privilege must be used.
You need to create the DLP policy to meet the technical requirements.
What should you configure first?

