1. Testlet 1
Case Study
This is a case study. Case studies are not timed separately. You can use as much exam times as you would like to complete each case. However, there may be additional studies and sections on this exam. You must manage your time to ensure that you are able to complete all questions included on this exam in the time provided.
To answer the questions included in a case study, you will need to reference information that is provided in the case study. Case studies might contain exhibits and other resources that provide more information about the scenario that is described in the case study. Each question is independent of the other questions in this case study.
At the end of this case study, a review screen will appear. This screen allows you to review your answers and to make changes before you move to the next section of the exam. After you begin a new section, you cannot return to this section.
To start the case study
To display the first question in this case study, click the Next button . Use the buttons in the left pane to explore the content of the case study before you answer the questions. Clicking these buttons displays information such as business requirements, existing environment, and problem statements. When you are ready to answer a question, click the Question button to return to the question.
Overview
Existing Environment
Fabrikam, Inc. is a distribution company that has 500 employees and 100 contractors.
Active Directory
The network contains an Active Directory forest named fabrikam.com. The forest is synced to Microsoft Azure Active Directory (Azure AD). All the employees are assigned Microsoft 365 E3 licenses.
The domain contains a user account for an employee named User10.
Client Computers
All the employees have computers that run Windows 10 Enterprise. All the computers are installed without Volume License Keys. Windows 10 license keys are never issued.
All the employees register their computer to Azure AD when they first receive the computer.
User10 has a computer named Computer10.
All the contractors have their own computer that runs Windows 10. None of the computers are joined to Azure AD.
Operational Procedures
Fabrikam has the following operational procedures:
- Updates are deployed by using Windows Update for Business.
- When new contractors are hired, administrators must help the contactors configure the following settings on their computer:
- User certificates
- Browser security and proxy settings
- Wireless network connection settings
Security policies
The following security policies are enforced on all the client computers in the domain:
- All the computers are encrypted by using BitLocker Drive Encryption (BitLocker). BitLocker recovery information is stored in Active Directory and Azure AD.
- The local Administrators group on each computer contains an enabled account named LocalAdmin.
- The LocalAdmin account is managed by using Local Administrator Password Solution (LAPS).
Problem Statements
Fabrikam identifies the following issues:
- Employees in the finance department use an application named Application1. Application1 frequently crashes due to a memory error. When Application1 crashes, an event is written to the application log and an administrator runs a script to delete the temporary files and restart the application.
- When employees attempt to connect to the network from their home computer, they often cannot establish a VPN connection because of misconfigured VPN settings.
- An employee has a computer named Computer11. Computer11 has a hardware failure that prevents the computer from connecting to the network.
- User10 reports that Computer10 is not activated.
Technical requirements
Fabrikam identifies the following technical requirements for managing the client computers:
- Provide employees with a configuration file to configure their VPN connection.
- Use the minimum amount of administrative effort to implement the technical requirements.
- Identify which employees’ computers are noncompliant with the Windows Update baseline of the company.
- Ensure that the service desk uses Quick Assist to take remote control of an employee’s desktop during support calls.
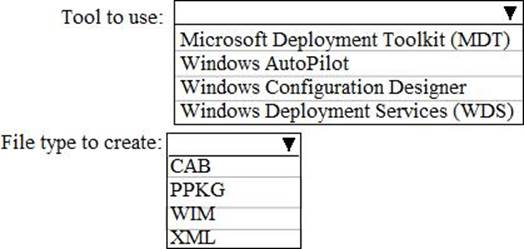
- Automate the configuration of the contractors’ computers. The solution must provide a configuration file that the contractors can open from a Microsoft SharePoint site to apply the required configurations.
HOTSPOT
You need to implement a solution to configure the contractors’ computers.
What should you do? To answer, select the appropriate options in the answer area. NOTE: Each correct selection is worth one point.