New CyberSec First Responder Exam CFR-310 Dumps Questions | 2020 DumpsBase
To be CyberSec First Responder certified to certify that you have the knowledge, skills, and abilities required to deal with a changing threat landscape and will be able to assess risk and vulnerabilities, acquire data, perform analysis, continuously communicate, determine scope, recommend remediation actions, and accurately report results. New CFR-310 dumps questions at DumpsBase have been released for CyberSec First Responder (CFR) certification today. It must be clear that CFR-310 CyberSec First Responder exam dumps contain real exam questions and accurate answers, you can read DumpsBase CFR-310 exam dumps questions in pdf file and free software to pass CFR-310 exam in the first try.
CFR-310 Exam Is A New Version For CyberSec First Responder (CFR) Instead OF CFR-210
Obviously, cybersecurity professionals require a well-rounded understanding of the tools, processes, and strategies that can be employed to defend their information systems from constantly evolving threats. A CyberSec First Responder is the first line of defense against cyber attacks that can cost an organization valuable time and money. The CyberSec First Responder certification program will prepare security professionals to become the first responders who defend against cyber attacks by teaching students to analyze threats, design secure computing and network environments, proactively defend networks, and respond/investigate cyber security incidents.
Most candidates are familiar with CFR-210 CyberSec First Responder certification exam. However, CFR-210 version of CyberSec First Responder exam has been retired in Septembe of 2019. New CyberSec First Responder certification CFR-310 exam was launched in September of 2018, all future candidates and current candidates must take and pass the updated exam, CFR-310 in order to hold a valid CyberSec First Responder certification.
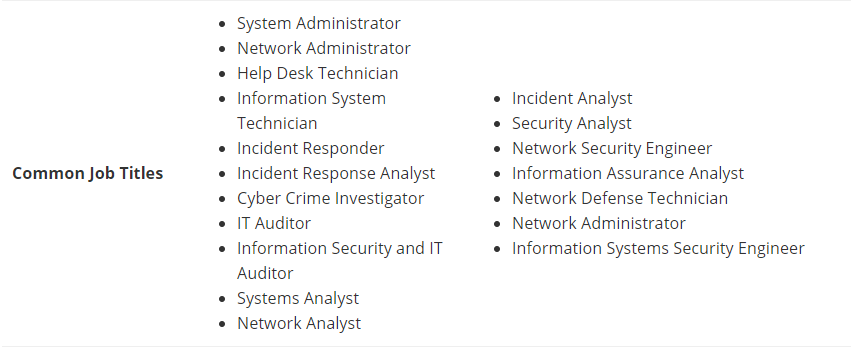
CyberSec First Responder CFR-310 Exam Is Good For Being More Job Titles
CyberSec First Responder Certification exam is design for individuals with between 3 and 5 years of experience working in a computing environment as part of a CERT/CSIRT/SOC who protect critical information systems before, during, and after an incident. Successfully completing CyberSec First Responder CFR-310 Exam is good for being more job titles as we shown in the picture:
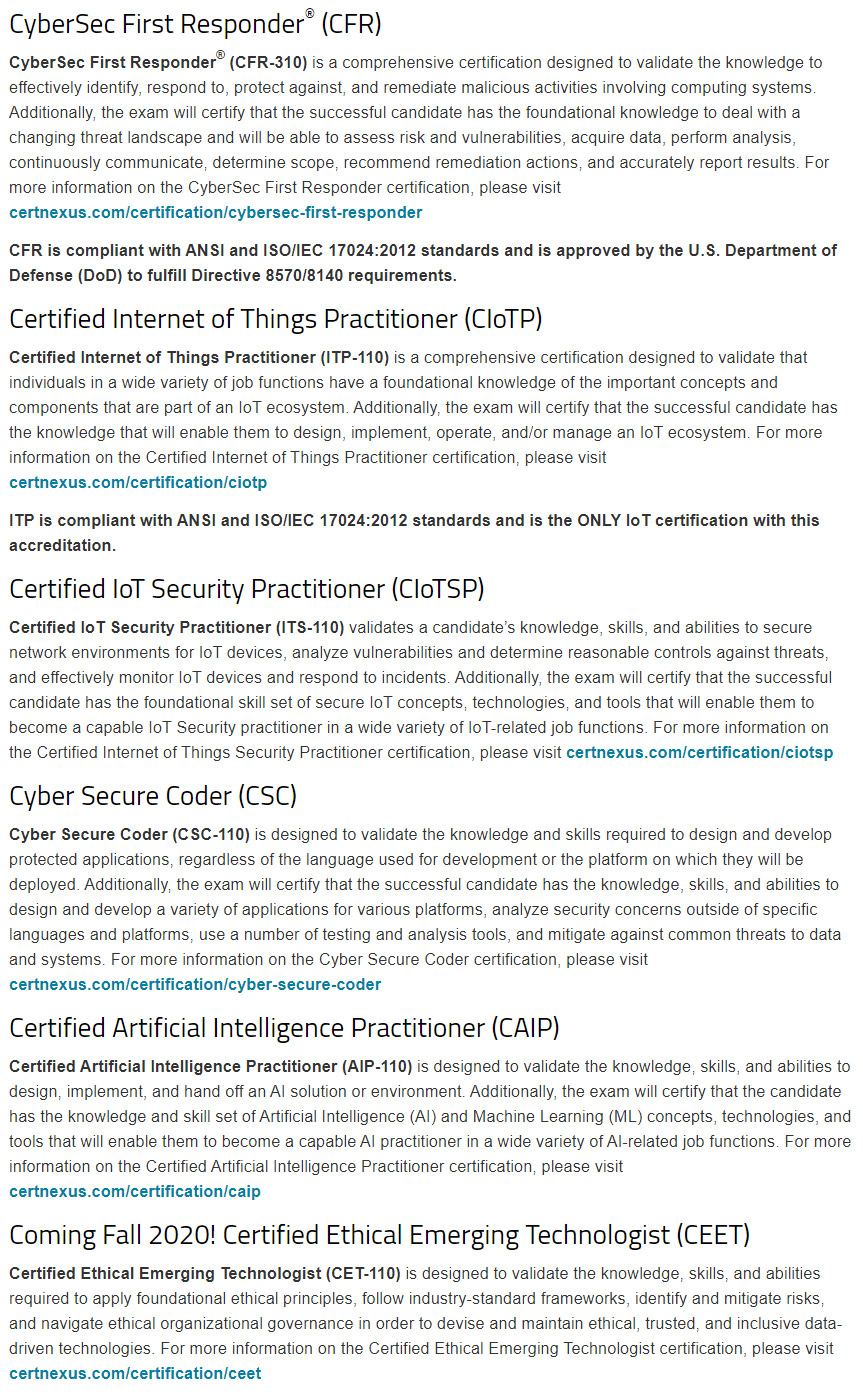
CyberSec First Responder (CFR) CFR-310 Exam Is One OF CertNexus Certification Exams
We know CertNexus certifications, which understands that the success of an organization depends upon all its people as the global purveyor of vendor neutral, emerging technology certifications and micro-credentials. CyberSec First Responder (CFR) CFR-310 Exam is one of the CertNexus Certification exams containing 100 real exam questions and answers. Candidates should be answer CFR-310 exam for CyberSec First Responder certification in 120 minutes at Pearson VUE. Get 70% or 71% score tio pass, depending on exam form.
Pass CyberSec First Responder (CFR) CFR-310 Exam With DumpsBase Good Questions Today
Get DumpsBase good exam questions to pass CyberSec First Responder (CFR) CFR-310 Exam today. New CyberSec First Responder Exam CFR-310 Dumps Questions from DumpsBase are great, we ensure that you can pass CFR-310 exam smoothly. We have CFR-310 exam questions free online for checking.
A network security analyst has noticed a flood of Simple Mail Transfer Protocol (SMTP) traffic to internal clients. SMTP traffic should only be allowed to email servers.
Which of the following commands would stop this attack? (Choose two.)
A. iptables -A INPUT -p tcp –dport 25 -d x.x.x.x -j ACCEPT
B. iptables -A INPUT -p tcp –sport 25 -d x.x.x.x -j ACCEPT
C. iptables -A INPUT -p tcp –dport 25 -j DROP
D. iptables -A INPUT -p tcp –destination-port 21 -j DROP
E. iptables -A FORWARD -p tcp –dport 6881:6889 -j DROP
Answer: AC
A cybersecurity expert assigned to be the IT manager of a middle-sized company discovers that there is little endpoint security implementation on the company’s systems.
Which of the following could be included in an endpoint security solution? (Choose two.)
A. Web proxy
B. Network monitoring system
C. Data loss prevention (DLP)
D. Anti-malware
E. Network Address Translation (NAT)
Answer: AB
A Linux system administrator found suspicious activity on host IP 192.168.10.121. This host is also establishing a connection to IP 88.143.12.123.
Which of the following commands should the administrator use to capture only the traffic between the two hosts?
A. # tcpdump -i eth0 host 88.143.12.123
B. # tcpdump -i eth0 dst 88.143.12.123
C. # tcpdump -i eth0 host 192.168.10.121
D. # tcpdump -i eth0 src 88.143.12.123
After imaging a disk as part of an investigation, a forensics analyst wants to hash the image using a tool that supports piecewise hashing.
Which of the following tools should the analyst use?
A. md5sum
B. sha256sum
C. md5deep
D. hashdeep
Answer: A
Which of the following is a cybersecurity solution for insider threats to strengthen information protection?
A. Web proxy
B. Data loss prevention (DLP)
C. Anti-malware
D. Intrusion detection system (IDS)
Answer: B
A security administrator is investigating a compromised host.
Which of the following commands could the investigator use to display executing processes in real time?
A. ps
B. top
C. nice
D. pstree
Answer: B
A system administrator identifies unusual network traffic from outside the local network.
Which of the following is the BEST method for mitigating the threat?
A. Malware scanning
B. Port blocking
C. Packet capturing
D. Content filtering
Answer: C
Which of the following technologies would reduce the risk of a successful SQL injection attack?
A. Reverse proxy
B. Web application firewall
C. Stateful firewall
D. Web content filtering
Answer: B
An incident responder has collected network capture logs in a text file, separated by five or more data fields.
Which of the following is the BEST command to use if the responder would like to print the file (to terminal/ screen) in numerical order?
A. cat | tac
B. more
C. sort –n
D. less
Answer: C
Which of the following characteristics of a web proxy strengthens cybersecurity? (Choose two.)
A. Increases browsing speed
B. Filters unwanted content
C. Limits direct connection to Internet
D. Caches frequently-visited websites
E. Decreases wide area network (WAN) traffic
Answer: AD
